Having set up the openLDAP server and we have seen how to do this on Raspberry Pi, SUSE and Ubuntu. We now turn our attention to authenticating Ubuntu Linux clients to the central directory. These clients could be Linux desktops or servers. In the video we use a Raspberry Pi openLDAP server and a Ubuntu 13.04 ldap client.
Create Posix Users and Groups
We must first make sure that we have Posix users and groups in the Directory. We can add users and groups using the ldapadd command and ldif files.
Creating a group
The LDIF file to create a group will be normally be quite small, it does not have many attributes.
dn: cn=ldapusers,ou=groups,dc=tup,dc=com objectClass: posixGroup cn: ldapusers gidNumber: 4000
Here we create the ldapusers group in the group OU.
Creating posix users
POSIX users are users that authenticate to Linux and have the required attributes. A sample account can be seen below where we create the Mike account to belong to the ldapusers group we created before:
dn: uid=mike,ou=people,dc=tup,dc=com objectClass: inetOrgPerson objectClass: posixAccount objectClass: shadowAccount uid: mike sn: smith givenName: mike cn: mike uidNumber: 4000 gidNumber: 4000 userPassword: Password1 loginShell: /bin/bash homeDirectory: /home/mike
With the file or files created we can add the users with
ldapadd -W -D cn=admin,dc=tup,dc=com -f users.ldif
If we are on the ldap server we can omit the -H for the host.
Ubuntu Client
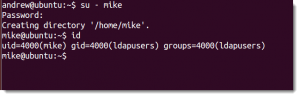
If we now want to log in as the user Mike from the Ubuntu client we need to configure LDAP authentication from Ubuntu 13.04
sudo apt-get install ldap-auth-client nscd
The install will start and run through the basic configuration wizard. We can always run trough the wizard later if we need to make changes. To run the wizard again if changes need to be made later the wizard is accessed as:
sudo dpkg-reconfigure ldap-auth-config
With the wizard complete it will have written to /etc/ldap.conf. We now need to configure the name service file, /etc/nsswitch.conf. This we do by running the following command:
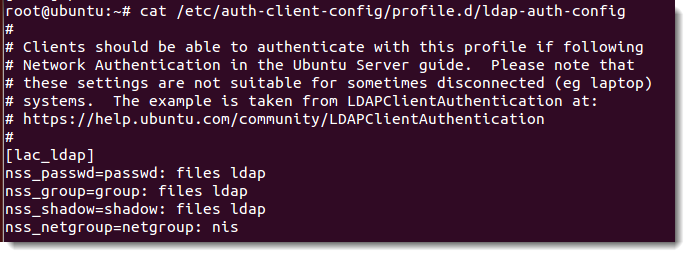
sudo auth-client-config -t nss -p lac_ldap
This will setup the nss profile to search for local users then ldap users. See the file /etc/auth-client-config/profile.d/ldap-auth-config for more details
If we do not have a central file server for home directories we will need to create users’ home directories locally when they log in. PAM, the plugable authentication modules can do this. Create a configuration file in /usr/share/pam-configs/ . It should read similar to the following
Name: activate mkhomedir Default: yes Priority: 900 Session-Type: Additional Session: required pam_mkhomedir.so umask=0022 skel=/etc/skel
We are now ready to update pam:
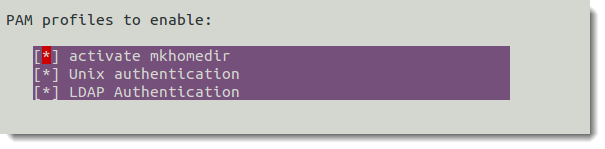
sudo pam-auth-update
This will start a little wizard, make sure your configuration shows, along with LDAP and anything else that you need. They normally will be selected.
Finally we just need to restart the name cache daemon:
sudo /etc/init.d/nscd restart
We can test the results by running
getent passwd
We should see the ldap users and groups listed. We can now login as Mike, in my case, from the command line using a full login from a TTY or using su. The login from the GUI display manager we need to make another adjustment and this will be in another tutorial.