Using RBAC and Roles in oracle Solaris 11 is designed around the least privileged security model. Giving users the minimum rights they need to be able to accomplish their task. I am always shocked by how many system administrators are prepared to give developers the root password because they ask for it! In this tutorial we will look at how we can use to root role without having access to the root password and how we can create least privileged roles with just the rights needed.
Roles
The root user is a role rather than a typical user in Oracle Solaris 11. This means that users do not lo in directly as this account. Users may still use the Substitute User , su, command to gain privileges of the role but they can only use su to switch to the role is the role has previously be assigned to them. In this way we have additional security:
- Root user cannot login directly
- Users, even knowing the root password can only user the role if it is assigned to them
Role Passwords
It is normal that you authenticate to the role using the role password. If we do not want to tell users the role password then we can set authentication to prompt for the user’s own password, similar to the way sudo can be used.
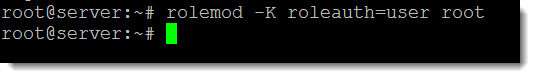
rolemod -K roleauth=user root rolemod -K roleauth=role root
The first example will require the users own password when switch to the root role. the second example will require the password of the role itself.
Least Privileged
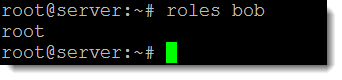
If we check the roles assigned to the user bob using the following command:
roles bob
We can see he has been assigned the root role. It is possible that he does not need all of the permissions and the concept of assigning the minimum rights should always be the aim. Let’s assume that he just needs to create and manage user accounts then, although the root role is more than sufficient it opens security hole if bob should do more than he should.
Profiles
Profiles in Solaris 11 RBAC allow authorizations and privileged commands to be grouped together and can be assigned to users or to roles. If assigned to a user the user may carry out those tasks directly whereas is a privilege is assigned to a role the user will ‘su’ to the role to gain privileges. To list all profiles we can use the command:
profiles -a | more
From the output we can see there is a profile called “User Management”. To print information on this profile we can use the command:
profiles -p “User Management” info
We can see the details listed in the graphic and several authorities and commands are included in the profile. Any user or roles with this profile will have the authority to carry out these tasks.
Create a role
If we want to create a role to represent these rights we can user the command roleadd:
roleadd -m -P “User Management” -K roleauth=user usrman
Here we create the role, named usrman, we require the user password rather than the role password as authentication, roleauth=user, and we use the profile mentioned, -P “User Management”. We cannot set the role password when we have user authentication set.
Assign role to user
The role now can be assigned to the user bob:
usermod -R +usrman bob
Bo will now be able to su to the role and use only the commands he needs.