 A system that has a, pretty much, out-of-the-box configuration is unlikely to be the most secure system on the block. Although Linux is, in general, a secure operating system there is still much to tune. As with any OS, the security is very much driven by how the system is managed.
A system that has a, pretty much, out-of-the-box configuration is unlikely to be the most secure system on the block. Although Linux is, in general, a secure operating system there is still much to tune. As with any OS, the security is very much driven by how the system is managed.
In the last section we looked at how we could disable ICMP on the system to help obscure the system from network pings. ICMP is a feature that works with IPv4 and not IPv6. Our IPv4 “obscured” host can still be discovered via IPv6. The host discovery mechanism is different in IPv6 to IPv4 as is the operation of the ping6 command.
Each objective is available to view online. However if you prefer to have all the content in one place and study from an eBook then the objective ‘LPIC 3 Linux Security 326.1 Host Hardening’ is now available to download for just £0.99.
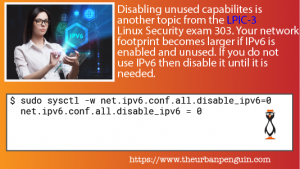
If you are not using IPv6, or at least knowingly using IPv6, then you should turn off IPv6 and only enable it again when you need to deploy services on IPv6. If you have IPv6 enabled but you are not using it, the security focus is never on IPv6 or vulnerablities associated with it. Malicious exploits may be happening on your system without your knowledge. Disabling of IPv6 may be implemented via Kernel options at boot time or using sysctl. For the moment we will use sysctl. Later we will look more at GRUB2 and how we pass Kernel options at boot time.
First, to ping a host with IPv6, we will start by confirming that ICMP responses are disabled and IPv4 pings fails to the local host:
$ sysctl -ar 'icmp_echo.*allWe will now try to ping the IPv6 local host address, this used the ping6 command:
$ ping6 -c1 -I lo ::1 PING ::1(::1) from ::1 lo: 56 data bytes 64 bytes from ::1: icmp_seq=1 ttl=64 time=0.037 ms --- ::1 ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 0.037/0.037/0.037/0.000 msTo view the IPv6 addresses assigned to all interfaces we can use the command ip:
$ ip -6 a 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 state UNKNOWN qlen 1 inet6 ::1/128 scope host valid_lft forever preferred_lft forever 2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1450 state UP qlen 1000 inet6 fe80::f816:3eff:fe50:bf35/64 scope link valid_lft forever preferred_lft foreverIf we needed to see only IPv4 addresses then change -6 to -4. Using ping6 we can see that we can still use IPv6 to discover the server. Futhermore, we can discover hosts on the network by connecting to the All Hosts Anycast Group ff02::1. An IPv6 feature allowing access to all available IPv6 hosts. I only have one host on the network, but if we had more and the firewall allowed IPv6 over the network we would be able to see more results:
$ ping6 -I eth0 ff02::1 PING ff02::1(ff02::1) from fe80::f816:3eff:fe50:bf35%eth0 eth0: 56 data bytes 64 bytes from fe80::f816:3eff:fe50:bf35%eth0: icmp_seq=1 ttl=64 time=0.042 msThese are great features but if you are not using IPv6 you should disable it as part of any basic security audit. Disabling IPv6 now does not prevent it from being re-enabled when and if you need it in the future.
To check the current configuartion we will use sysctl:
$ sudo sysctl -ar ipv6.conf.all.disable
net.ipv6.conf.all.disable_ipv6 = 0Disable IPv6
To disable IPv6 we can change the value to 1:
$ sudo sysctl -w net.ipv6.conf.all.disable_ipv6=1 net.ipv6.conf.all.disable_ipv6 = 1With IPv6 disabled the system will not be contactable or discoverable via the protocol. If we check the ip command again:
$ ip -6 aWe see no addresses assigned to the loopback or any other device.
net.ipv4.icmp_echo_ignore_all = 1 $ ping -c1 localhost PING localhost (127.0.0.1) 56(84) bytes of data. --- localhost ping statistics --- 1 packets transmitted, 0 received, 100% packet loss, time 0ms
We will now try to ping the IPv6 local host address, this used the ping6 command:
To view the IPv6 addresses assigned to all interfaces we can use the command ip:
If we needed to see only IPv4 addresses then change -6 to -4. Using ping6 we can see that we can still use IPv6 to discover the server. Futhermore, we can discover hosts on the network by connecting to the All Hosts Anycast Group ff02::1. An IPv6 feature allowing access to all available IPv6 hosts. I only have one host on the network, but if we had more and the firewall allowed IPv6 over the network we would be able to see more results:
These are great features but if you are not using IPv6 you should disable it as part of any basic security audit. Disabling IPv6 now does not prevent it from being re-enabled when and if you need it in the future.
To check the current configuartion we will use sysctl:
$ sudo sysctl -ar ipv6.conf.all.disable
net.ipv6.conf.all.disable_ipv6 = 0
Disable IPv6
To disable IPv6 we can change the value to 1:
With IPv6 disabled the system will not be contactable or discoverable via the protocol. If we check the ip command again:
We see no addresses assigned to the loopback or any other device.
