[custom-header-login]
Running CGI scripts on an Apache HTTPD server may be as simple as running a BASH shell script, PERL script or back-end PHP. There is a risk though that the scripts may be tampered with locally or though malicious access from the web server. In which case who knows what the scripts may do. Implementing CGI security with mod_suexec ensures a few things:
- The directory the scripts are located in can only we written to by the suexec user. No other account. this means that the script cannot be deleted and a replacement rogue script added with the same name
- The script cannot be writable by any other user than the suexec user
- The script directory and script must be owned by the script user and script group
- The script user cannot be a sup user or member of the root group
- The script cannot have the SUID or GUID permission set
The system does co out of its way to ensure best security is maintained. To implement this:
- Create a script user in a private group. There is no need to set password and perhaps could set shell to /bin/false
- Create a script directory outside of the DocumentRoot and change the ownership to the scriptuser and scriptgroup
- Set the permissions to 755
- Add scripts to this directory and ensure ownership and permissions are the same as directory
- Add SuexecUserGroup scriptuser scriptuser to the httpd.conf
- Ensure the mod_alias.so, mod_cgi.so and mod_suexec.so are loaded from the httpd.conf
- Create an alias allowing access to the script directory
- Define the directory block with Options +ExceCGI and SetHandler cgi-script .
- restart apache
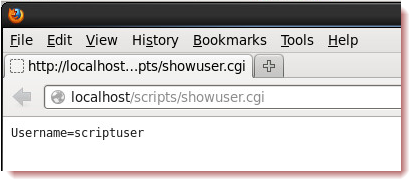
A sample cgi-script shows that the script runs as the script user:
#!/bin/bash echo "Content-type: text/plain" echo "" echo "Username="`whoami`
Whoami is in back-ticks not quotes.
If 500 errors occur check the log file /var/log/httpd/suexec.log